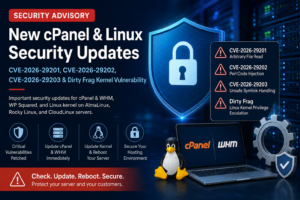
New cPanel and Linux Kernel Security Advisory: What Website Owners and Server Admins Should Do Now
Published: May 2026
Advisory focus: cPanel and WHM, WP Squared, AlmaLinux, Rocky Linux, CloudLinux, VPS and dedicated servers
Severity: High to Critical
Action required: Update cPanel, update the kernel, reboot where required, verify the running versions
A new set of security updates has been released for cPanel and WHM, WP Squared, and Linux kernel based hosting environments. These updates are important for anyone running a VPS, dedicated server, reseller hosting node, or shared hosting environment with cPanel.
This advisory follows our earlier post, Critical Linux Hosting Security Advisory covering cPanel, Apache, OpenSSH, Kernel and CloudLinux. That earlier update covered several serious issues across the Linux hosting stack. The latest round adds three new cPanel security vulnerabilities and a Linux kernel vulnerability commonly referred to as Dirty Frag.
If you manage your own server, you should review this advisory carefully and take action immediately. If your server is managed by WebCare360, our technical team is already reviewing affected systems and applying the required security updates according to the scope of your service.
For customers who want managed help with patching, monitoring, and server hardening, our 托管服务 include expert support for VPS, dedicated server, and offshore hosting environments.
What Has Happened?
cPanel published security updates for three new vulnerabilities affecting cPanel and WHM, and WP Squared. The vulnerabilities are tracked as:
CVE-2026-29201
CVE-2026-29202
CVE-2026-29203
According to cPanel’s security update, patched cPanel and WHM versions include 11.136.0.9, 11.134.0.25, 11.132.0.31, 11.130.0.22, 11.126.0.58, 11.124.0.37, 11.118.0.66, 11.110.0.116, 11.110.0.117, 11.102.0.41, 11.94.0.30, 和 11.86.0.43 or newer. WP Squared is patched from 11.136.1.10 and newer. (support.cpanel.net)
At the same time, cPanel also published guidance for Dirty Frag, a Linux kernel vulnerability affecting several hosting focused operating systems, including AlmaLinux, Rocky Linux, CloudLinux and Ubuntu versions commonly used on hosting servers. (support.cpanel.net)
This means server owners need to check two separate areas:
The cPanel and WHM version
The active running Linux kernel
Updating packages alone is not always enough. For kernel vulnerabilities, the server must be rebooted into the fixed kernel before the system should be considered protected.
Why This Matters for Hosting Customers
Security issues in cPanel and the Linux kernel matter more in hosting environments than on many single user systems.
A shared hosting or reseller server may have many local users, website accounts, PHP applications, cron jobs, CMS installations, and control panel users. If one website is compromised, attackers often try to move further by abusing local privileges, weak file permissions, vulnerable control panel features, or outdated kernels.
That is why vulnerabilities involving file access, code injection, permission changes, and local privilege escalation should be treated seriously.
The practical risks include:
Unauthorized access to sensitive files
Privilege escalation from a lower level account
Service disruption or denial of service
Abuse of local user permissions
Higher risk after a website level compromise
Even if your website is online and working normally, the server may still be exposed if cPanel or the kernel has not been updated.
CVE-2026-29201: Arbitrary File Read in cPanel
CVE-2026-29201 is an arbitrary file read vulnerability in cPanel. The issue is related to insufficient validation in the feature::LOADFEATUREFILE adminbin call. cPanel states that this could allow an authenticated user to read arbitrary files. (support.cpanel.net)
For hosting providers, this is important because authenticated users are common on shared and reseller systems. A vulnerability does not always need to be remotely exploitable by the public internet to be dangerous. On multi user systems, authenticated user level bugs can still create real risk.
CVE-2026-29202: Perl Code Injection in cPanel
CVE-2026-29202 is a Perl code injection vulnerability involving the create_user API call and the plugin parameter. cPanel’s public update describes this as a privilege escalation issue. (support.cpanel.net)
Code injection vulnerabilities are serious because they can allow an attacker to influence how server side logic is executed. In a control panel environment, that can become especially sensitive due to how closely the panel is tied to account creation, permissions, and system level management.
CVE-2026-29203: Unsafe Symlink Handling
CVE-2026-29203 involves unsafe symlink handling. cPanel describes the issue as allowing a user to change permissions on an arbitrary file with chmod, which may result in denial of service or possible privilege escalation. (support.cpanel.net)
File permission bugs are particularly concerning on shared hosting systems. Hosting security depends heavily on separation between users, safe file ownership, hardened permissions, and correct isolation. Any flaw that weakens these boundaries must be patched quickly.
Dirty Frag: Linux Kernel Local Privilege Escalation
Dirty Frag is a Linux kernel vulnerability that may allow a local user to escalate privileges to root. cPanel’s advisory lists affected operating systems including CloudLinux 7 Hybrid, AlmaLinux and Rocky Linux 8, CloudLinux 8, AlmaLinux and Rocky Linux 9, CloudLinux 9, AlmaLinux 10, CloudLinux 10, and Ubuntu 20.04, 22.04 and 24.04. (support.cpanel.net)
AlmaLinux has published fixed kernel baselines for AlmaLinux 8, 9 and 10. AlmaLinux 8 is patched in kernel-4.18.0-553.123.2.el8_10 and newer. AlmaLinux 9 is patched in kernel-5.14.0-611.54.3.el9_7 and newer. AlmaLinux 10 is patched in kernel-6.12.0-124.55.2.el10_1 and newer. (AlmaLinux OS)
For hosting servers, this is critical because many systems provide some form of local user access, even if restricted. A compromised website, vulnerable plugin, weak SSH account, or abused local user can become a starting point for privilege escalation if the kernel is vulnerable.
How to Check Your cPanel Version
Log in to your server as root and run:
/usr/local/cpanel/cpanel -V
cat /usr/local/cpanel/version
Your version should be at or above the fixed version for your cPanel branch.
例如
11.134.0.25 or newer
11.136.0.9 or newer
If your server is below the fixed version, update cPanel:
/scripts/upcp --force
After the update completes, verify again:
/usr/local/cpanel/cpanel -V
cat /usr/local/cpanel/version
If needed, restart cPanel services:
/scripts/restartsrv_cpsrvd --hard
/scripts/restartsrv_queueprocd
Check the update log for errors:
tail -200 /var/cpanel/updatelogs/latest
grep -Ei "error|failed|failure|fatal|could not" /var/cpanel/updatelogs/latest | tail -50
If the server does not update to the expected version, check whether the update tier is pinned:
cat /etc/cpupdate.conf
How to Check Whether Dirty Frag Is Fixed
The most important command is:
uname -r
This shows the kernel the server is actually running.
For AlmaLinux 8, Rocky Linux 8, or CloudLinux 8, a fixed kernel should be at least:
4.18.0-553.123.2.el8_10.x86_64
For AlmaLinux 9, Rocky Linux 9, or CloudLinux 9, a fixed kernel should be at least:
5.14.0-611.54.3.el9_7.x86_64
For AlmaLinux 10 or CloudLinux 10, check against your vendor’s latest published fixed build. AlmaLinux lists the fixed AlmaLinux 10 baseline as:
6.12.0-124.55.2.el10_1
To see installed kernel packages:
rpm -q kernel-core | sort -V | tail
To see which kernel is selected for the next boot:
grubby --default-kernel
If the fixed kernel is installed but uname -r still shows an older version, reboot the server.
reboot
After the reboot, check again:
uname -r
How to Update the Kernel
On AlmaLinux, Rocky Linux, or CloudLinux based servers, run:
dnf clean all
dnf update 'kernel*' -y
Then reboot:
reboot
After the server comes back online:
uname -r
Do not skip the reboot. Kernel fixes are not active until the system is running the patched kernel, unless you are using a live patching product such as KernelCare and have confirmed that the relevant patch is applied.
Temporary Mitigation for Dirty Frag
If a patched kernel is not available yet, cPanel recommends a temporary mitigation involving the esp4, esp6, 和 rxrpc kernel modules. This mitigation should be used carefully because it may affect systems using IPsec, strongSwan, Libreswan, or other VPN services that rely on ESP modules. (support.cpanel.net)
Create the mitigation file:
cat > /etc/modprobe.d/dirtyfrag.conf <<'EOF'
install esp4 /bin/false
install esp6 /bin/false
install rxrpc /bin/false
EOF
Unload the modules if they are currently loaded:
rmmod esp4 esp6 rxrpc 2>/dev/null || true
Clear cached pages:
sync
echo 3 > /proc/sys/vm/drop_caches
Verify:
lsmod | egrep '^(esp4|esp6|rxrpc)'
cat /etc/modprobe.d/dirtyfrag.conf
If the lsmod command returns no matching modules, the mitigation is active.
This is not a permanent replacement for patching. The best fix is still to install and boot into the patched kernel.
Recommended Security Checklist
Use this checklist if you manage your own VPS or dedicated server.
1. Update cPanel and WHM
/scripts/upcp --force
/usr/local/cpanel/cpanel -V
2. Update the Kernel
dnf clean all
dnf update 'kernel*' -y
3. Reboot if the Kernel Was Updated
reboot
4. Confirm the Running Kernel
uname -r
5. Review cPanel Logs
grep -Ei "%0a|%0d|\\.\\./|%2e%2e|LOADFEATUREFILE|create_user|plugin=|chmod|symlink" \
/usr/local/cpanel/logs/access_log | tail -50
grep -Ei "panic|fatal|permission denied|LOADFEATUREFILE|create_user|plugin|symlink|chmod" \
/usr/local/cpanel/logs/error_log | tail -50
6. Review Root and SSH Access
last -a | head -50
cat /root/.ssh/authorized_keys
awk -F: '($3 == 0) {print}' /etc/passwd
Normally, only root should have UID 0.
7. Restrict Control Panel Access Where Possible
cPanel and WHM ports should not be exposed broadly unless necessary.
Common ports include:
2082
2083
2086
2087
2095
2096
Where possible, restrict WHM access to trusted administrator IP addresses.
What WebCare360 Is Doing
At WebCare360, we treat hosting security advisories as operational priorities, not routine announcements. Our team reviews affected services, validates fixed versions, checks running kernels after reboot, and monitors vendor advisories for follow up patches.
For managed environments, our work may include:
Updating cPanel and WHM to fixed builds
Checking cPanel update logs for failures
Installing fixed kernel packages
Rebooting systems when required
Confirming the running kernel after reboot
Reviewing suspicious cPanel access patterns
Checking for exposed administrative services
Applying temporary mitigations where appropriate
Monitoring vendor updates from cPanel, AlmaLinux and CloudLinux
If you operate an unmanaged server, these checks remain your responsibility. If you prefer our team to handle server patching, monitoring, and hardening, you can review our WebCare360 hosting services or contact support for assistance.
Customers using our VPS solutions can also review our 离岸 VPS 托管 options, while customers who need full hardware isolation and higher performance can explore our 专用服务器.
Final Recommendation
If your server runs cPanel, WHM, WP Squared, AlmaLinux, Rocky Linux, or CloudLinux, do not assume it is safe just because automatic updates are enabled.
Check it manually.
/usr/local/cpanel/cpanel -V
uname -r
A server should only be considered remediated when cPanel is on a fixed build and the server is running a patched kernel.
This advisory is part of our ongoing security coverage for Linux hosting customers. For background on the earlier related vulnerabilities, read our previous post: Critical Linux Hosting Security Advisory for cPanel, Apache, OpenSSH, Kernel and CloudLinux.